Theoretically, GSM has been broken since 2003, but the limitations of hardware at the time meant cell phone calls and texts were secure from the prying ears of digital eavesdroppers and all but the most secret government agencies. Since then, the costs of hardware have gone down, two terabytes of rainbow tables have been published, and all the techniques and knowledge required to listen in on cell phone calls have been available. The only thing missing was the hardware.
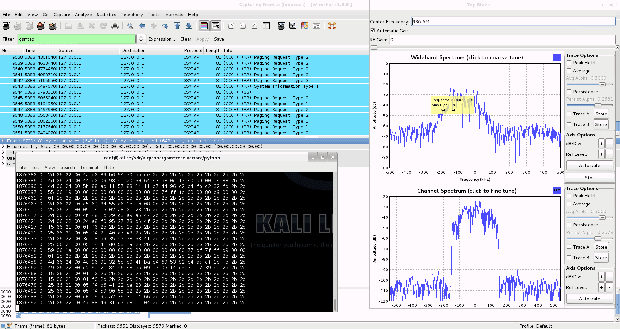
Now, with a super low-cost USB TV tuner come software defined radio, [domi] has put together a tutorial for cracking GSM with thirty dollars in hardware. Previous endeavours to listen in and decrypt GSM signals used fairly expensive software defined radios – USRP systems that cost a few thousand dollars a piece. Since the advent of RTL-SDR, the price of software defined radios has come down to about $30 on eBay, giving anyone with a Paypal account the ability to listen in on GSM calls and sniff text messages.
The process of cracking GSM first involves getting the TMSI – Temporary Mobile Subscriber Identifier – a unique ID for each phone in a certain cell. This is done by sending a silent SMS that will send back and acknowledgement an SMS has been received on the victim’s phone, but won’t give the victim any indication of receiving a message. From there, the attacker listens to the GSM signals in the cell, receiving bursts attached to a TMSI, and cracking the encrypted stream using 1.6 TB of rainbow tables.
[domi] put up a four-part tutorial series (part 1 above; part 2, part 3, and part 4) that goes over the theory and the actual procedure of cracking text messages and voice calls with a simple USB TV tuner. There are a few limitations; the attacker must be in the same cell as the victim, and it looks like real-time voice decoding isn’t yet possible. Cracking GSM for $30, though, that’s good enough for us.
Now, with a super low-cost USB TV tuner come software defined radio, [domi] has put together a tutorial for cracking GSM with thirty dollars in hardware. Previous endeavours to listen in and decrypt GSM signals used fairly expensive software defined radios – USRP systems that cost a few thousand dollars a piece. Since the advent of RTL-SDR, the price of software defined radios has come down to about $30 on eBay, giving anyone with a Paypal account the ability to listen in on GSM calls and sniff text messages.
The process of cracking GSM first involves getting the TMSI – Temporary Mobile Subscriber Identifier – a unique ID for each phone in a certain cell. This is done by sending a silent SMS that will send back and acknowledgement an SMS has been received on the victim’s phone, but won’t give the victim any indication of receiving a message. From there, the attacker listens to the GSM signals in the cell, receiving bursts attached to a TMSI, and cracking the encrypted stream using 1.6 TB of rainbow tables.
[domi] put up a four-part tutorial series (part 1 above; part 2, part 3, and part 4) that goes over the theory and the actual procedure of cracking text messages and voice calls with a simple USB TV tuner. There are a few limitations; the attacker must be in the same cell as the victim, and it looks like real-time voice decoding isn’t yet possible. Cracking GSM for $30, though, that’s good enough for us.
0 comments:
Post a Comment